Social networks and digital media continue to increase their relevance in our daily lives, which is why organizations and companies need solutions capable of analyzing, in real time, the events that occur and may affect them. This preventive nature improves the ability to react to an adverse event and supports strategic decision-making.
We understand Cyberintelligence as the product generated through a process of acquisition, processing, analysis, and dissemination of information that identifies, tracks, and predicts threats, risks, and opportunities in cyberspace, in order to support decision-making.
Every hour, thousands of news items and opinions are published on the Internet referring to people, companies, services, products, institutions, and organizations, etc. Being aware of this and being able to track the information published about an entity that may be affected is part of what is known as online reputation management.
It must be kept in mind that this is not simply a systematic compilation, but the acquisition and analysis of information to assess whether the content affects the reputation of the entity under study, enabling measures to be taken in the early stages of these campaigns.
The platform developed by Internet Security Auditors:
Monitor
Through probes across different media and social networks, detecting and alerting in real time about information, comments, criticism, or mentions that may affect the brand’s digital reputation, 24x7.
Analyze
Being able to search, view, analyze, and classify any type of content, regardless of the source of information or its format (texts, videos, audio, or images).
Assess
Using reputation-oriented criteria, any publication that makes reference to the brands under monitoring.
The client defines the brands (names and logos) as well as the information sources, which include social networks, dark web, messaging systems, data leaks, etc., the characteristics such as the alert system, and requirements such as languages or geographic scope, among many other operating and working parameters for the monitoring process.
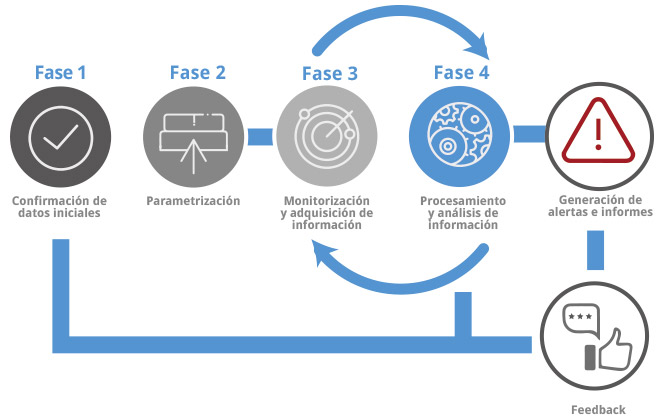
The Digital Brand Monitoring service is carried out in the following phases:
Before starting the monitoring of the specified brands, Internet Security Auditors will request confirmation of the monitoring scope and all characteristics, based on recommendations that cover the client’s needs.
Once the scope characteristics are confirmed, our digital monitoring platform will be parameterized based on these characteristics, as well as the requirements determined by the client.
The monitoring process will be constant throughout the lifetime of the project. Our platform monitors the selected information sources and detects those publications or interactions that may affect the brands specified in the scope.
This is the most complex phase of the process, since the monitoring platform does not simply compile information systematically; it does much more, using highly efficient artificial intelligence processing. In addition, the Cyberintelligence analysts team improves the processing and results so that:
- The communication of false positives is avoided, reducing the number of communications and alerting only in those cases that are truly necessary.
- Information is obtained about the disseminator of the publication, assessing their credibility.
- The real impact of the threat is estimated based on the information obtained and the characteristics of the disseminator, determining their influence capacity or the potential impact of the threat.
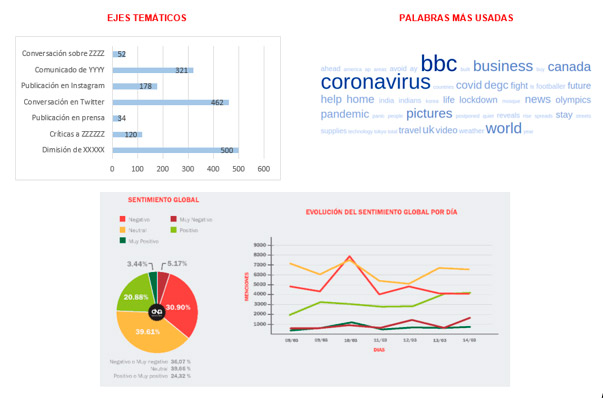
Based on the information collected, detailed reports are generated describing the information related to the alert, reflecting the level of criticality of each publication (depending on the level of impact), which helps prioritize corrective measures and the response to be taken.