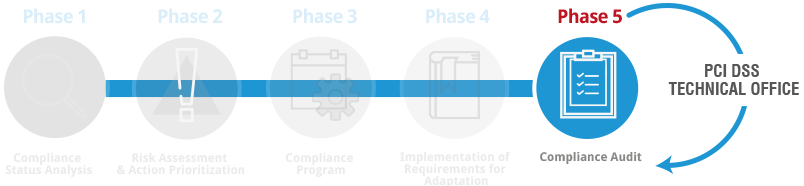
The on‑site Compliance Audit is mandatory for Level 1 Merchants (more than 6,000,000 transactions) and Level 1 Service Providers (more than 300,000 transactions), and must be carried out by a company certified as a QSA (Qualified Security Assessor) by the PCI SSC — a certification held by Internet Security Auditors.
It is recommended for any company that, although not required to undergo audits, wants an independent QSA auditor to verify that it has achieved compliance or continues to meet the security requirements mandated by PCI DSS.
At the start of the project, a meeting will be held with the team selected by the client, with the purpose of:
- Introducing the audit team.
- Explaining the scope of the Audit.
- Identifying the project manager(s).
- Emphasizing the confidential nature of the Audit.
- Addressing any questions regarding the Audit process.
During this phase, the processes carried out by the client in their daily operations related to the transmission, processing, or storage of credit card data will be reviewed. The objective is to verify the accuracy, correctness, and absence of changes in the compliance environment since the initial PCI DSS implementation or since the last audit performed.
This review will involve:
- Reviewing credit card data flows.
- Reviewing the information assets (HW, SW, Networks, Applications, Databases, etc.) involved in the transmission, processing, and storage of credit card data, their interrelationships, and the security measures currently implemented.
- Reviewing relationships with third parties (service providers) and how they impact PCI DSS compliance..
All these tasks will require meetings with department or area managers, as well as the technical personnel designated by the client.
- Completing the analysis of the compliance environment to ensure that the scope matches what was initially defined for the subsequent PCI DSS compliance validation.
- Performing the documentation review associated with the implementation of the standard.
Additionally, a service provider or merchant may rely on a third party; therefore, any outsourced services will be analyzed by reviewing the documentation related to the service delivery conditions or contractual agreements.
The necessary tasks will be carried out to define the audit sample, prepare the work plan with the meeting schedule, and execute the compliance tests required to obtain evidence. In addition, aspects such as specific personnel that may be needed for certain audit activities will be identified.
During this stage, the Audit Plan,is executed, carrying out the assessment of the controls implemented by the client to meet PCI DSS requirements, including the evaluation of compensating controls.
The Audit will be based on:
- Documentation analysis
- Compliance testing based on sampling
- Interviews with the Client’s personnel
The final result of the Audit is the so‑called Compliance Report. The audited entity must follow the reporting requirements of each payment card brand to ensure that each brand acknowledges the entity’s compliance status. According to the PCI SSC guidelines for version 3.2 of the compliance reports, its content will include the following:
1. Contact Information and Report Date:
1.1. Contact Information
1.2. Audit Date and Timeframe
1.3. PCI DSS Version
1.4. Additional Services Provided by the QSA
2. Summary:
2.1. Description of the entity’s payment card business
2.2. High‑level network diagram(s)
3. Description of the Scope of Work and Approach Adopted
3.1. QSA validation of scope accuracy
3.2. Environment on which the Audit is focused
3.3. Network segmentation
3.4. Network segmentation details
3.5. Connected entities involved in processing
3.6. Other business entities requiring PCI DSS compliance
3.7. Wireless network summary
3.8. Wireless network details
4. Details of the Audited Environment
4.1. Detailed network diagram(s)
4.2. Description of payment card data flows
4.3. Payment card data storage
4.4. Critical hardware within the cardholder data environment
4.5. Critical software within the cardholder data environment
4.6. Sampling
4.7. Sample sets for the report
4.8. Service providers and third parties with whom cardholder data is shared
4.9. Third‑party payment applications/solutions
4.10. Documentation reviewed
4.11. Personnel interviewed
4.12. Managed service providers
4.13. Summary of compensating control justifications
4.14. Summary of justifications for controls not tested
5. Quarterly Scan Results
5.1. Quarterly Scan Results – initial PCI DSS compliance validation
5.2. Quarterly Scan Results – subsequent PCI DSS compliance validations
5.3. Scan compliance certificates
6. Resultados y Observaciones
At the end of the project, a presentation of the Compliance Report and the Audit results will be conducted, reviewing the identified deficiencies, strengths, key aspects, and improvement proposals, all of which will be reflected in the final documentation.