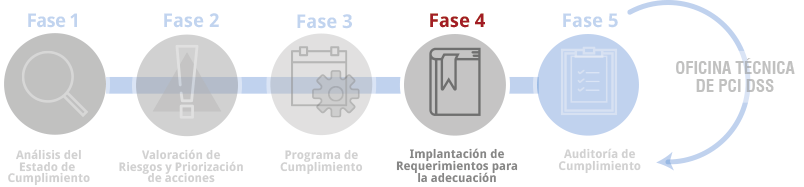
The Implementation of Requirements for Remediation executes the compliance program for the non‑conformities identified in previous phases, carrying out the consulting and advisory activities needed for any task required to achieve PCI DSS compliance.
The implementation phase is the most intensive stage in the PCI DSS Compliance Process and encompasses all activities within the Compliance Program required by the PCI DSS requirements.
In this phase, the relevant consulting, technical, and organizational activities will be carried out to ensure the organization can successfully pass a subsequent audit or compliance validation.
In summary, the key aspects covered in this phase will be the following:
Main Regulatory Framework
Drafting of the Security Policy, procedures for the use of critical technologies, PCI DSS regulatory framework, CDEM inventory, etc.
PCI DSS Risk Analysis
Drafting of the methodology and execution of the specific Risk Assessment for those controls that allow flexibility in execution frequency.
Management of firewalls, routers, and IDS/IPS systems
Drafting and/or review of procedures for management, rule review, usage matrix, etc.
Secure System Management
Drafting of secure configuration procedures for systems, customized hardening guides, and support for system hardening, etc.
Secure Network Architecture Design
Review and improvement proposals for security, scope reduction, and protection related to the network architecture and communications within the PCI DSS environment.
Analysis of Data Repositories and Payment Data Processing
Drafting of policies for the search, retention, and deletion of payment data, creation of data inventories and access matrices, etc.
Encryption Key Management
Drafting of key management procedures, review of the encryption mechanisms and key management practices in use, etc.
Change Management
Drafting of change management procedures and security testing procedures for network and system environments, preparation of administrative templates, etc.
Security Update Management
Drafting/review of security update methodologies, drafting of specific procedures related to the identification and management of vulnerabilities and patches, etc.
System Synchronization
Review of the system synchronization architecture and time distribution, drafting of procedures, system review, etc.
Log Management, Monitoring, HIDS and FIM
Drafting/review of log management and review procedures, assessment of critical files, and definition/creation of procedures and documentation related to monitoring, alert identification, definition of procedures for monitoring platforms and review testing, development of dashboards, etc.
Logical Access Control
Review and definition of Access Controls, identification and use of two‑factor authentication systems, drafting of Logical Access Control procedures, creation of access matrices and password management procedures, identification/definition of the architecture for the use of Identity Management and Single Sign‑On solutions, etc.
Media Storage Management
Drafting/review of media handling procedures and implementation processes.
Security Management with Vendors and Third Parties
Drafting/review of vendor management procedures, third‑party contracts within the CDE, vendor matrices, contractual compliance reviews of vendors, etc.
Human Resources Management
Adaptation of HR procedures to PCI DSS.
Security Incident Management
Drafting/review of Incident Response procedures, management of incidents with the Payment Brands, review and improvement of Incident Response Plans, plan execution and definition of improvements to the response, etc.
Periodic Audit Program
Drafting/review of review procedures, definition of schedules and activities based on internal and external requirements, vulnerability analysis, ethical hacking, etc.
Definition of Metrics and Indicators for PCI DSS
Identification of Metrics and Indicators for Dashboards, creation of the necessary documentation aligned with ISO 27004 and PCI DSS.
Software Management and Development
Definition and creation of Secure Software Development Guidelines, code reviews and application audits, procedures for implementing Security in Software, and training for development teams.
Training
Definition and creation of training materials by personnel group and responsibilities, delivery of awareness and technical training, creation of training documentation, and definition of knowledge‑validation processes. Internet Security Auditors will also provide full support for resolving incidents or activities that may arise during the implementation tasks